Spyzie is a reliable application used for hacking Instagram passwords and monitoring the accounts. The best feature of Spyzie is that it has a Keylogger facility. The beauty of this facility is that you get information of every key typed in by the target (intentionally as well as unintentionally) in your computer. This requires you to install the Spyzie app on the target’s phone as well. The target is not aware of this installation because the application is a hidden one. Let us now look at the procedure to follow for hacking Instagram account password using Spyzie.
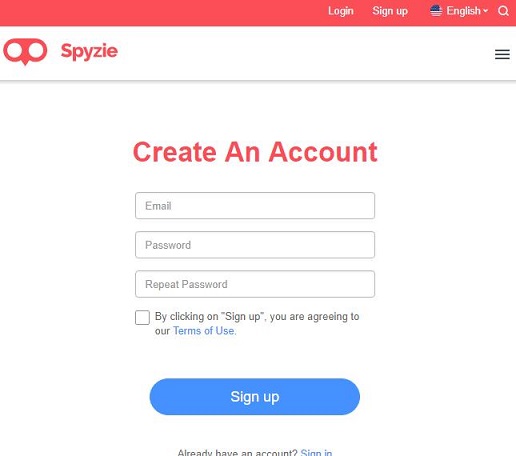
Step 1: Register for an account with Spyzie.com.
Step 2: You get a confirmation mail from Spyzie that contains links to control panel and your log in details as well.
Step 3: Go ahead and install Spyzie on the target’s phone. The demo can help you with the installation process.
Step 4: On successful installation, you will be able to access the same from the control panel.
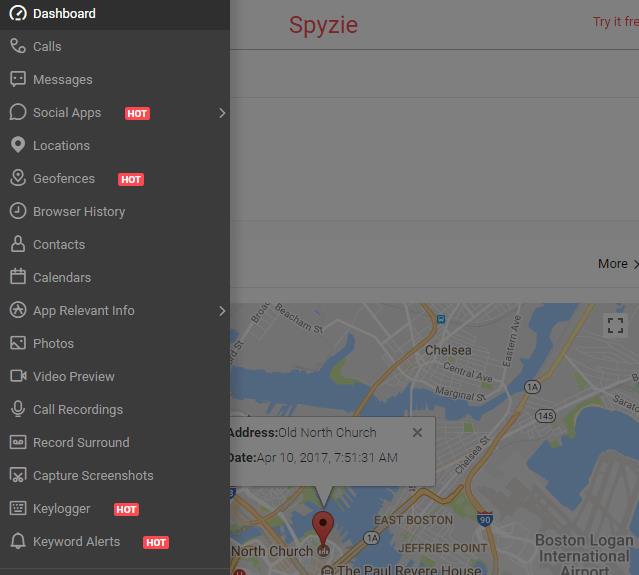
Step 5: Log in to your Spyzie account using the log in details provided in the confirmation mail.
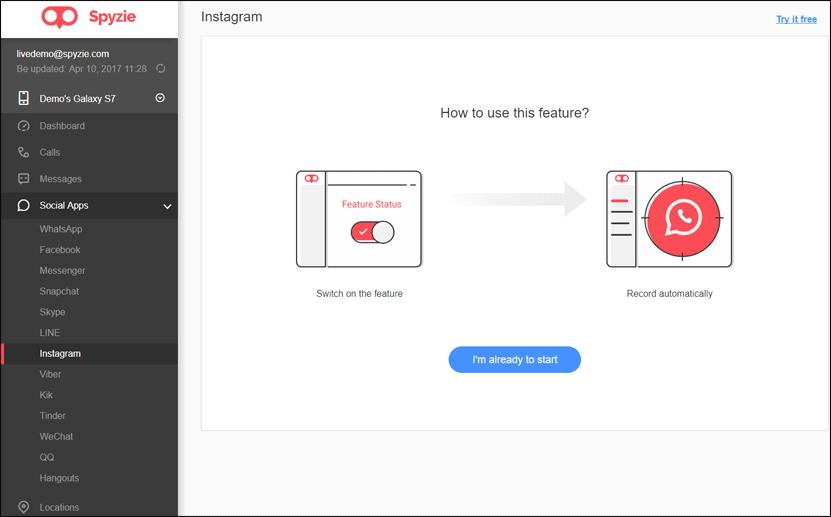
Step 6: Access the Keylogger option and procure information about every keystroke used by the target.
Step 7: Wait for the target to access Instagram. You will get the alerts on time. The Keylogger plays its part to perfection by procuring the password for you. Use the password to access the target’s Instagram account from your computer. Monitor his / her activities without the target’s knowledge.
Comments
Post a Comment